Cari obat di Farmaku










What Is Wsiaccount -
Kirim Dari

Farmaku Siliwangi • Semarang Kota
 Dijamin Ori
Dijamin Ori Instan
Instan Garansi 7 Hari
Garansi 7 HariInformasi Produk
Kategori
Golongan
Berat Pengiriman (±)
5 gr
Harus Disertai Resep Dokter, Produk ini membutuhkan resep dokter, harap unggah resep dokter pada saat pembelian!
Deskripsi Produk
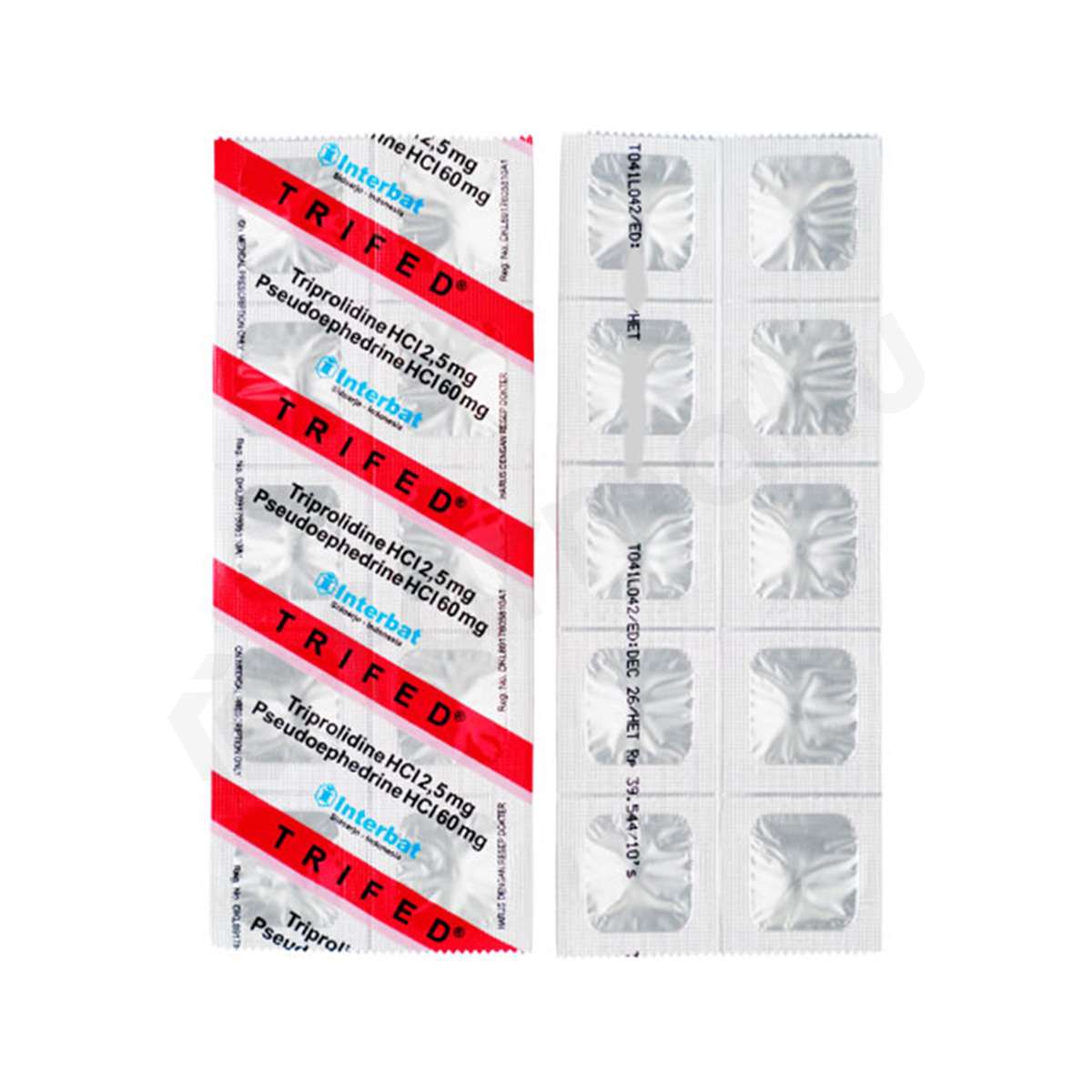
Trifed
Trifed digunakan untuk meredakan gejala flu, pilek, dan rhinitis alergi. Obat ini mengandung senyawa aktif triprolidine HCl dan pseudoephedrine HCl. Senyawa aktif triprolidine HCl termasuk dalam...
Produk Serupa
What Is Wsiaccount -
Consider the modern corporation. It runs on automation. Backups must run at 2:00 AM. Databases must sync with cloud storage. Emails must be sent automatically when a customer fills out a form. These actions cannot be performed by a human employee (who is asleep or on vacation), nor can they be performed by the "Administrator" account (which has the digital equivalent of a master key to the entire building). To solve this, IT architects create "service accounts." The WSIAccount is one of these digital butlers. It has just enough privilege to install software on a specific server or to shuttle data between a web form and a database, but not enough to delete the entire company payroll.
So, the next time you see a strange, uncapitalized compound word in a system log, do not dismiss it as gibberish. Recognize it for what it is: a digital fossil, a piece of internal shorthand that escaped its cage and became a de facto standard. The WSIAccount is the internet’s reminder that even in a world of artificial intelligence and quantum computing, much of our digital lives still run on the equivalent of sticky notes left by a tired programmer in 2005. what is wsiaccount
At its most concrete level, "WSIAccount" is an abbreviation. In the world of enterprise software and server management, it typically stands for or, in some contexts, Web Service Integration Account . To the uninitiated, this sounds like jargon. But to a system engineer, it is a character in a silent play—a non-human user, a robotic actor designed to perform a very specific set of chores. Consider the modern corporation
Furthermore, the existence of WSIAccount highlights a profound tension in cybersecurity: the conflict between convenience and security. A default account name is convenient for a developer, but it is a beacon for a hacker. If an attacker compromises a server and sees a process running under "wsiaccount," they immediately know that account is used for installation or integration. They know it likely has elevated, yet specific, privileges. It becomes a target. Consequently, modern security best practices demand that administrators rename or disable the default WSIAccount and replace it with a unique, obfuscated name. The ghost must be exorcised to survive. Databases must sync with cloud storage
The truth is, WSIAccount does not have a Wikipedia page. It is not a product you can buy, nor a viral trend you can follow. Instead, "wsiaccount" is a fascinating piece of digital archaeology; a technical placeholder that reveals how modern computing is held together by invisible conventions, legacy codes, and the quiet genius of service architecture.
Ultimately, asking "What is wsiaccount?" is like asking "What is a 'John Doe'?" It is a placeholder. It is a linguistic hack. It is a testament to the fact that the digital world is not built from scratch every day, but rather layered upon legacy decisions made two decades ago. The WSIAccount is the quiet, invisible screw holding together the server rack in the basement—a screw that no one thinks about until the whole shelf collapses.
In the vast, humming ecosystem of the internet, we are all accustomed to digital identities. We have Facebook profiles for our social lives, Gmail accounts for our correspondence, and Steam IDs for our gaming alter egos. But every so often, a term surfaces from the technical underbelly of the web—a phrase that feels simultaneously specific and alien. "WSIAccount" is one such ghost. Ask a dozen IT professionals what it is, and you might get a dozen blank stares, followed by one quiet administrator who sighs, "Oh, that ."
Lainnya Dari Brand Ini
Lihat semuaBrand Terpopuler
Kategori Terpopuler
 Konsultasi Dokter
Konsultasi Dokter 



